Blog
FACET-ing New Relic PageViewTiming Data By 'Page Type'
Published: November 7, 2024
New Relic’s PageViewTiming data set provides excellent visibility into important performance metrics such as Core Web Vitals. When analyzing this data it can be useful to segment it by “page type” — for example, on an ecommerce website it can be helpful to know LCP or CLS scores for the product detail page, or product listing page individually. While it’s possible to view performance metrics for specific page URLs via the default pageUrl field, a website can have thousands (or more) of unique URLs for a given page type. Unless a predictable and consistent pattern is used for all URLs of a specific page type, by default it is not possible to segment data this way.
Add an IP Address to a Fastly ACL via the CLI with Magento
Published: July 20, 2023
Recently I was in a bit of a pickle on a new Magento project that my company was taking over.
Access to the staging site was restricted via Fastly. I had SSH access to the environment, but my IP address was not allowed via the ACL, so I couldn’t connect to the website’s backend UI to grant myself access.
I wound up figuring out how to manage this via the CLI. Since I struggled a bit with figuring this out I figured I’d shared my findings here.
What CURLOPT_FAILONERROR does in PHP
Published: April 12, 2023
Testing for this blog post was done with PHP version 8.2.1
During a recent code review I learned about CURLOPT_FAILONERROR for the first time.
I read through both the libcurl documentation as well as the PHP documentation and in the end was still unclear exactly what this option does.
In this post I’ll share my findings from some experimentation.
Experimenting with Partytown
Published: December 22, 2022
A couple weeks back in a Twitter conversation I learned about Partytown.
Would you try to leverage the script off the main thread with Partytown?
— Denis Metzler (@DenisMetzler) December 13, 2022
Didn't use myself yet. Curious about your result.https://t.co/49ifl6QX7I
I was immediately intrigued by the idea and saw great potential, especially on the ecommerce projects that I work on on a daily basis.
Today I spent some time playing with Partytown. In this post I’ll share my process and findings.
Magento + OneTrust Cookie Consent - require is not a function
Published: December 20, 2022
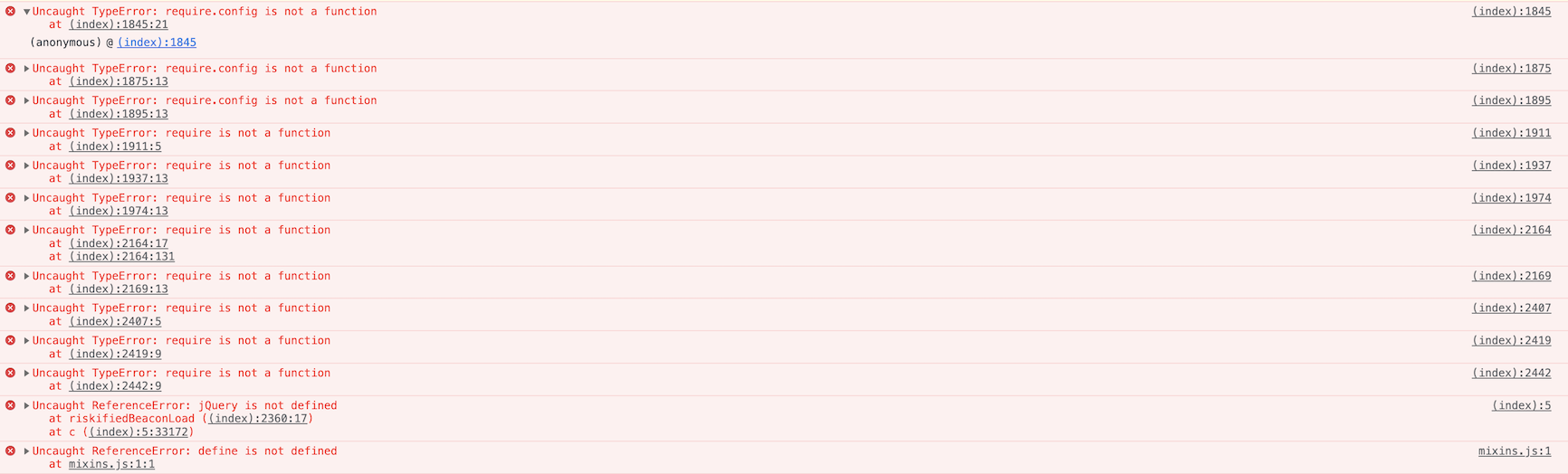
There’s a lot to be said about implementing OneTrust Cookie Consent and this post doesn’t intend to cover it all. Instead, I’d like to share my experience with the JavaScript errors that occured when adding the OneTrust Cookie Consent scripts to a production Magento instance. Here’s a screenshot of the errors from the developer tools:
How Magento's JavaScript Block Loader Works
Published: December 11, 2022
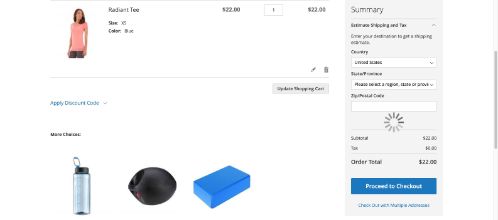
I’ve been looking at a Magento site where multiple loaders show up in different areas on the cart page. The loaders look something like this:
I did a bit of a deep dive into what actually causes these loader to show up. In this post I’ll share my findings.